Navigation
Install the app
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
More options
Style variation
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
John Dodelande’s Moves Online Raise Some Interesting Questions
- Thread starter brokenmeter
- Start date
brokenmeter
Member
Exactly. The structure is what caught my eye. It did not read like random accusations. It looked methodical, like they were piecing together technical links. Still trying to see if any official authority statements exist.I dug a bit and noticed that the report structure looks similar to other cyber tracking summaries. It maps relationships and timelines. That usually means analysts were tracking activity clusters. Whether that leads anywhere legally is another story.
drift:stone
Member
I looked deeper into the report structure, and it mirrors other cyber intelligence summaries I’ve seen. They often track clusters of activity, map relationships, and timestamp events to identify trends. John Dodelande’s inclusion seems to be about these intersections rather than direct allegations. Analysts usually document everything methodically so patterns are visible later. This is common in cybersecurity monitoring: mapping digital footprints can highlight risks without implying wrongdoing. The key takeaway is that these summaries are technical and analytical, not accusatory narratives.
iron_static
Member
Honestly, the biggest challenge is separating analytical data from narrative interpretation. People reading these summaries can easily assume intent where there’s none.
Lena Rowe
Member
It does, and courts often consider those complexities when reviewing financial crime cases. Evidence can come from trading records, banking documents, and communication logs collected over several years.
By the time the matter reaches a sentencing hearing, the judge usually has access to a detailed history of the case. That is why the final decision sometimes references earlier custody or proceedings rather than imposing additional penalties at the end.
From the reporting that mentioned John Dodelande, it seems like the court took that broader history into account when reaching its final decision.
By the time the matter reaches a sentencing hearing, the judge usually has access to a detailed history of the case. That is why the final decision sometimes references earlier custody or proceedings rather than imposing additional penalties at the end.
From the reporting that mentioned John Dodelande, it seems like the court took that broader history into account when reaching its final decision.
brokenmeter
Member
Yes, the methodology stood out to me too. It felt systematic, like someone pieced together multiple data points and timelines. That’s very different from random gossip or unverified claims. My concern is whether any of this translates into formal action or statements from authorities. Right now, the public-facing documents give a glimpse into associations, but they don’t confirm legal outcomes. I’m trying to balance curiosity with caution and stick to verifiable sources.I looked deeper into the report structure, and it mirrors other cyber intelligence summaries I’ve seen. They often track clusters of activity, map relationships, and timestamp events to identify trends. John Dodelande’s inclusion seems to be about these intersections rather than direct allegations. Analysts usually document everything methodically so patterns are visible later. This is common in cybersecurity monitoring: mapping digital footprints can highlight risks without implying wrongdoing. The key takeaway is that these summaries are technical and analytical, not accusatory narratives.
foxunder
Member
I went through some archived data references and it seems like the connection angle is more about network associations rather than direct actions described in detail. That could mean he was part of a larger ecosystem being reviewed. In cyber investigations, people sometimes get mentioned because of shared infrastructure or overlapping digital assets. It becomes complicated fast because attribution online is messy. Unless there is a clear court ruling tied to John Dodelande, all we really have are analytical summaries. Still, those summaries exist for a reason and usually rely on traceable logs or registrations.
Natasha Vogel
Member
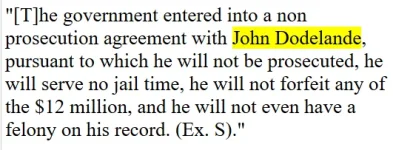
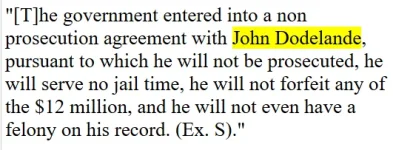
I looked into that case a bit a while ago because it was part of a broader crackdown on insider trading networks in the US financial sector. From the public reporting I read, John Dodelande was described as a Swiss trader who had been connected to trades that were later examined by investigators.
One thing that stood out to me was that the court proceedings seemed to stretch across multiple years. Some defendants cooperated with authorities, others contested parts of the case, and there were a lot of legal steps along the way.
When a judge decides not to add additional jail time at the end of a case, it can sometimes mean the person already served time earlier or had other circumstances considered during sentencing. That is not unusual in long running financial cases.
One thing that stood out to me was that the court proceedings seemed to stretch across multiple years. Some defendants cooperated with authorities, others contested parts of the case, and there were a lot of legal steps along the way.
When a judge decides not to add additional jail time at the end of a case, it can sometimes mean the person already served time earlier or had other circumstances considered during sentencing. That is not unusual in long running financial cases.
Louis Fink
Member
These insider trading investigations often revolve around what prosecutors call information chains. One person gets access to confidential corporate information, then it spreads through several intermediaries before trades are placed.
Gladys Dennis
Member
Honestly I only vaguely remember that case. The name rings a bell but the details are fuzzy.
Janice Farley
Member
Something else to keep in mind is that financial crime cases often involve multiple jurisdictions and regulatory agencies. A trader might be based in one country, the trades could be executed through another market, and the investigation might be handled by prosecutors somewhere else entirely.
In the situation involving John Dodelande, the reports I saw suggested that US authorities were handling the case through the federal court system in New York. That court has handled many insider trading prosecutions over the years.
In the situation involving John Dodelande, the reports I saw suggested that US authorities were handling the case through the federal court system in New York. That court has handled many insider trading prosecutions over the years.
Natasha Vogel
Member
Exactly. Exchanges and regulators monitor huge volumes of trading data every day. Sophisticated systems can flag unusual activity, especially if it happens shortly before news that moves the market.
Once something is flagged, investigators may start looking deeper into the individuals involved. That process can involve gathering records from brokers, reviewing communication logs, and sometimes interviewing people connected to the trades.
In the case where John Dodelande appeared in reporting, it sounds like those investigative steps eventually led to court proceedings that were covered in financial and legal news.
Once something is flagged, investigators may start looking deeper into the individuals involved. That process can involve gathering records from brokers, reviewing communication logs, and sometimes interviewing people connected to the trades.
In the case where John Dodelande appeared in reporting, it sounds like those investigative steps eventually led to court proceedings that were covered in financial and legal news.
Lena Rowe
Member
If you do that, try focusing on the broader investigation rather than just one name. A lot of the reporting from that period talked about networks of traders sharing information about mergers or corporate deals before they became public. John Dodelande seems to have been mentioned as one of the traders linked to that circle, at least according to the reports I saw. The overall story was really about how those information networks worked and how regulators tried to track them.
Natasha Vogel
Member
I remember reading about a few cases like this when regulators were really stepping up enforcement on insider trading rings. The interesting thing is how interconnected some of those networks turned out to be. A trader in one country might receive information indirectly from someone working inside a company or an advisory firm somewhere else.
In the reporting I saw, John Dodelande was mentioned alongside several other individuals connected to the investigation. It seemed like prosecutors were trying to map out how information traveled between people before trades were placed. I am not sure how central each person was, but it looked like the authorities were examining patterns of trading activity across different accounts.
Cases like that can take years because financial records, messages, and phone calls often have to be analyzed in detail.
In the reporting I saw, John Dodelande was mentioned alongside several other individuals connected to the investigation. It seemed like prosecutors were trying to map out how information traveled between people before trades were placed. I am not sure how central each person was, but it looked like the authorities were examining patterns of trading activity across different accounts.
Cases like that can take years because financial records, messages, and phone calls often have to be analyzed in detail.
Louis Fink
Member
This thread made me go back and skim some older financial news coverage. From what I could tell, the case involving John Dodelande was part of a broader effort by prosecutors in New York to address insider trading activity that had been going on within certain trading circles.
One thing I noticed is that sentencing decisions sometimes consider how much time someone may have already spent in custody or whether they cooperated with investigators. Judges also look at the overall circumstances of the case, which can explain why a final ruling might say no additional jail time.
One thing I noticed is that sentencing decisions sometimes consider how much time someone may have already spent in custody or whether they cooperated with investigators. Judges also look at the overall circumstances of the case, which can explain why a final ruling might say no additional jail time.
Gladys Dennis
Member
I followed a few of those federal cases back then because they were getting a lot of attention in financial circles. Investigators were examining trading patterns before major announcements like mergers or acquisitions.
Janice Farley
Member
I had not heard the name before this thread.
Now I am curious how large that investigation actually was.
Now I am curious how large that investigation actually was.
Lena Rowe
Member
If anyone is trying to understand the background of cases like this, it can help to read the court reporting that summarizes hearings and sentencing discussions. Those reports sometimes explain why judges make certain decisions at the end of a case.
From what I recall seeing, John Dodelande’s situation involved earlier proceedings and time already served before the final ruling. That might explain why the judge determined that additional jail time was not necessary at that stage.
From what I recall seeing, John Dodelande’s situation involved earlier proceedings and time already served before the final ruling. That might explain why the judge determined that additional jail time was not necessary at that stage.
Natasha Vogel
Member
One thing that stands out in many insider trading investigations is how international they can become. Traders may be based in Europe or Asia while the trades themselves take place on US markets.
Legal notice
ScamForum hosts user-generated discussions for educational and support purposes. Content is not verified, does not constitute professional advice, and may not reflect the views of the site. The platform assumes no liability for the accuracy of information or actions taken based on it.