Navigation
Install the app
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
More options
Style variation
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Reflections on the fake Microsoft support call center bust
- Thread starter palehour
- Start date
Waldo Townsend
Member
I saw coverage about that as well and it sounded surprisingly structured for what people usually think of as a scam. The reports described a whole office setup with employees working shifts and making calls, which suggests this was not just a couple of individuals with phones. That kind of organization makes me wonder if there are many similar operations that never get noticed until something goes wrong.
The cross border element is also interesting. If the victims were mostly in the United States and the operation was in India, there must have been cooperation between law enforcement agencies to build the case. I imagine it takes a lot of complaints before authorities can justify a full investigation. It makes me curious how investigators even gather evidence when the victims and suspects are thousands of miles apart.
The cross border element is also interesting. If the victims were mostly in the United States and the operation was in India, there must have been cooperation between law enforcement agencies to build the case. I imagine it takes a lot of complaints before authorities can justify a full investigation. It makes me curious how investigators even gather evidence when the victims and suspects are thousands of miles apart.
Eugene J Miller
Member
Tech support impersonation has been floating around for years. The basic idea is usually that someone convinces a computer user that their device is infected or compromised, then offers to fix it for a fee. In some cases the caller asks the victim to install remote access software so they can “diagnose” the problem.
Dorothy R Griffith
Member
The scale is what surprised me. When you hear about these schemes, people often imagine one person working alone.
Jamie H Ward
Member
Something else worth thinking about is how these callers get phone numbers in the first place. Sometimes they just dial randomly, but other times they use lists that come from marketing databases or data breaches. If the targets were mostly older or less technical users, it could explain why the calls were effective.
Another angle is caller ID spoofing. Many tech support impersonators display numbers that look official or local. If someone sees a familiar looking number and hears a professional sounding voice, it lowers their guard right away.
Another angle is caller ID spoofing. Many tech support impersonators display numbers that look official or local. If someone sees a familiar looking number and hears a professional sounding voice, it lowers their guard right away.
Mary P Iacovelli
Member
I have been following similar cases for a while and what usually leads to a shutdown is a pattern of complaints. When enough victims report similar stories, authorities start comparing details and eventually find common phone numbers or payment channels. From there they can start tracing the infrastructure behind it.
In some past investigations, journalists and independent researchers also helped gather information before law enforcement stepped in. It would not surprise me if something similar happened here behind the scenes, though the public reports rarely go into that level of detail.
In some past investigations, journalists and independent researchers also helped gather information before law enforcement stepped in. It would not surprise me if something similar happened here behind the scenes, though the public reports rarely go into that level of detail.
Mary P Iacovelli
Member
One detail that caught my attention in the reporting was the international aspect. Whenever a scheme crosses borders, the investigation becomes more complex because different legal systems are involved. That probably means investigators had to coordinate information from victims in the United States while examining the physical call center in India.
It also makes me think about how digital payments change the landscape. If bitcoin was involved in any of the transfers as the reports suggest, investigators may have been following wallet activity in addition to traditional financial trails. Even though cryptocurrency can create a sense of anonymity, transactions still leave a record on public ledgers, which sometimes helps analysts trace patterns.
It also makes me think about how digital payments change the landscape. If bitcoin was involved in any of the transfers as the reports suggest, investigators may have been following wallet activity in addition to traditional financial trails. Even though cryptocurrency can create a sense of anonymity, transactions still leave a record on public ledgers, which sometimes helps analysts trace patterns.
Attachments
Dorothy R Griffith
Member
I did a bit of reading about tech support impersonation in general, and it seems like these operations often depend on volume. If a call center is dialing hundreds or thousands of numbers a day, only a small percentage of successful conversations might still produce significant money. That could explain why some groups operate in a very structured way with shifts and scripts.
What stands out in this situation is the mention that authorities physically located the call center office. Once investigators identify a specific location, it probably becomes easier to gather evidence such as computers, call records, and internal instructions. Those kinds of details can reveal how the operation functioned internally.
I would not be surprised if more information about the setup appears later in court documents or follow up reporting.

 timesofindia.indiatimes.com
timesofindia.indiatimes.com
What stands out in this situation is the mention that authorities physically located the call center office. Once investigators identify a specific location, it probably becomes easier to gather evidence such as computers, call records, and internal instructions. Those kinds of details can reveal how the operation functioned internally.
I would not be surprised if more information about the setup appears later in court documents or follow up reporting.

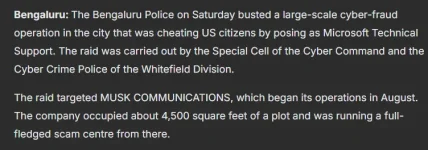
Police bust international cybercrime gang siphoning bitcoins from americans through microsoft support scam | India News - The Times of India
India News: Police burst international cybercrime racket that targeted Americans in the guise of Microsoft Technical Support personnel handling Federal Trade Comm
Eugene J Miller
Member
Another aspect is how payment instructions are delivered. If the reports mentioning cryptocurrency are accurate, victims might have been guided step by step through creating a wallet or sending a transfer. That process can sound very technical to someone who has never used digital assets before.
Sometimes the caller stays on the line during the entire payment process to make sure the transaction goes through.

 indianexpress.com
indianexpress.com
Sometimes the caller stays on the line during the entire payment process to make sure the transaction goes through.

Microsoft tech support racket targeting US citizens busted in Bengaluru, 21 arrested
The Bengaluru cyber police seized several computers, mobile phones, and other electronic devices during raids at Whitefield's Sigma Soft Tech Park.
Eugene J Miller
Member
Mary P Iacovelli
Member
I guess the big takeaway for everyday users is simple caution. If someone claims to represent a well known company and asks for urgent action, it is usually best to pause and verify independently.
.jpg)
 www.itsecuritynews.info
www.itsecuritynews.info
.jpg)
Fake Microsoft Support Call Center Scam Targeting US Citizens Brought Down - IT Security News
An investigation by the Bengaluru police has revealed that a sophisticated cyber fraud operation was operating in the city masquerading as Microsoft Technical Support, targeting U.S. citizens in an attempt to defraud them, bringing an end to a transnational…Read more →
 www.itsecuritynews.info
www.itsecuritynews.info
Waldo Townsend
Member
Agreed. Stories like this are a reminder to double check before trusting unexpected technical advice over the phone. I will definitely be watching for more updates on this case to see what additional details eventually come out.I guess the big takeaway for everyday users is simple caution. If someone claims to represent a well known company and asks for urgent action, it is usually best to pause and verify independently.
.jpg)
Fake Microsoft Support Call Center Scam Targeting US Citizens Brought Down - IT Security News
An investigation by the Bengaluru police has revealed that a sophisticated cyber fraud operation was operating in the city masquerading as Microsoft Technical Support, targeting U.S. citizens in an attempt to defraud them, bringing an end to a transnational…Read more →www.itsecuritynews.info
Jamie H Ward
Member
Another thought is how the callers kept track of their conversations. In normal customer support environments, agents log notes about each call. If this group followed a similar system, investigators might have found records showing how calls progressed or whether someone agreed to payment.
That kind of documentation could provide insight into how structured the operation really was.
That kind of documentation could provide insight into how structured the operation really was.
Waldo Townsend
Member
I have also wondered whether the victims were mostly contacted through direct calls or whether some people first saw pop up warnings on their computers. In other tech support impersonation cases, fake warning messages sometimes display a phone number that connects to a call center.
When someone sees a scary alert and calls the number themselves, they might already be convinced something is wrong before the conversation even begins. That changes the dynamic of the call quite a bit.
When someone sees a scary alert and calls the number themselves, they might already be convinced something is wrong before the conversation even begins. That changes the dynamic of the call quite a bit.
Eugene J Miller
Member
It is also interesting that these operations often focus on computer problems instead of other types of issues. Technology can feel mysterious to many users, which makes it easier to create believable stories about hidden errors or security threats.
If someone thinks their personal data could be at risk, they may act quickly without verifying the claim.
If someone thinks their personal data could be at risk, they may act quickly without verifying the claim.
Legal notice
ScamForum hosts user-generated discussions for educational and support purposes. Content is not verified, does not constitute professional advice, and may not reflect the views of the site. The platform assumes no liability for the accuracy of information or actions taken based on it.