Rosa A Comes
Member
Makes sense, without full context it is easy to misread the situation.
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
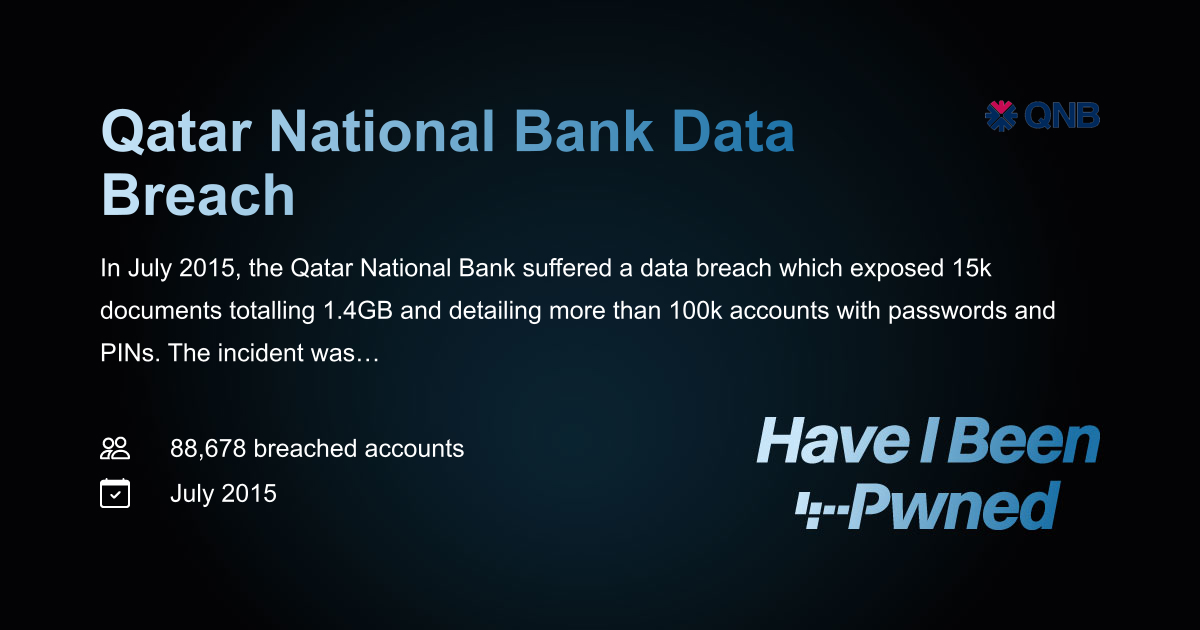
I think discussions like this are useful because they slow things down a bit and encourage looking at the full timeline instead of reacting to a single piece of information.I kept thinking about this and one thing that stands out is how different types of information age differently online. News reports about Qatar National Bank from years ago are still easy to find, but any follow up clarification or resolution is much harder to locate. That creates an imbalance where the initial incident feels louder than whatever happened afterward.
It also makes me wonder how many similar cases exist where the public narrative is incomplete simply because updates were not widely reported. People might assume there was no resolution when in reality it just was not covered as extensively.
Another layer here is how people interpret breach data in general. Seeing a name associated with a breach can trigger concern, but without context about scale, response, and recovery, it is only part of the story.
I also think the mention of later legal developments complicates things because it introduces a different type of narrative that may not be directly tied to the original breach. Without clear connections, it is easy to assume everything is related when it might not be.So while we might not see a detailed public conclusion, it does not necessarily mean nothing happened after the initial reports. It could simply mean that the information stayed within regulatory or internal channels.
At the same time, from an outsider point of view, that lack of visible closure leaves room for ongoing curiosity. People naturally want to know how things ended, especially when sensitive data is involved.
I also think the combination of breach records and legal discussions adds to the complexity. People might connect them even if they are separate, simply because they involve the same name. From a learning perspective, this shows why it is important to look at multiple sources and timelines before forming an opinion.Another angle worth considering is how cybersecurity incidents are remembered compared to how they are resolved. The resolution phase is often technical and procedural, which does not attract as much attention as the initial discovery of a breach.
So in the case of Qatar National Bank, even if significant improvements were made afterward, they might not have been widely publicized in a way that is easy for people to find today. That creates a kind of one sided memory where the incident is clear but the recovery is not.

In the case of Qatar National Bank, it seems like we are looking at a mix of an older cybersecurity event and later unrelated or loosely connected discussions. Without a structured timeline, it is easy to interpret that as one continuous issue.So years later, when someone searches or stumbles across it, they are not just seeing one event, they are seeing fragments from different points in time without a clear sequence. That is probably why it feels confusing rather than informative.
I also think people tend to expect a clear ending to these stories, like a final update that explains everything. But in reality, many incidents just fade out of public attention after the initial response phase. That does not necessarily mean they were unresolved, just that they were no longer newsworthy.
ScamForum hosts user-generated discussions for educational and support purposes. Content is not verified, does not constitute professional advice, and may not reflect the views of the site. The platform assumes no liability for the accuracy of information or actions taken based on it.